Cryptocurrency Hash Algorithm Comparison Tool
Compare Cryptocurrency Hash Algorithms
Compare key features of SHA-256, Keccak-256, BLAKE2b, Scrypt, and Equihash. Understand the trade-offs between speed, security, ASIC resistance, and energy efficiency.
Algorithm Comparison
| Algorithm | Speed | ASIC Resistance | Memory Usage | Energy Efficiency | Primary Use Cases |
|---|---|---|---|---|---|
| SHA-256 | Fast | Low | Low | Low (high energy) | Bitcoin RIPEMD-160 (addresses) |
| Keccak-256 | Moderate | Moderate | Moderate | Moderate | Ethereum Smart contracts |
| BLAKE2b | Very Fast | Moderate-High | Low | High (low energy) | Nano High-throughput networks |
| Scrypt | Moderate | Low (failed) | High | Low | Litecoin Legacy projects |
| Equihash | Slow | Low (failed) | Very High | Low | Zcash Legacy projects |
Key Insights
Speed vs. Security Trade-off
BLAKE2b is the fastest (1,200 MB/s), while SHA-256 is still very fast (500 MB/s). However, speed often comes at the cost of security.
Energy Efficiency Comparison
BLAKE2b consumes only 0.05 kWh per 1,000 transactions vs. SHA-256's 950 kWh for the same volume. This represents a 19,000x difference in energy efficiency.
ASIC Resistance Reality Check
Memory-hard algorithms (Scrypt, Equihash) were designed for ASIC resistance but have been overcome by specialized hardware. BLAKE2b offers the best balance of speed and ASIC resistance today.
Quantum Computing Threat
SHA-256 is vulnerable to quantum attacks in 10-15 years. SHA-3 (Keccak) offers better quantum resistance and is being adopted by Ethereum and future blockchains.
Which Algorithm Should You Choose?
Use this simple guide to decide which hash algorithm is best for your needs:
For Maximum Security
Choose Keccak-256 (SHA-3 variant) for its quantum resistance and sponge construction. Best for long-term security where future-proofing matters.
Recommended for Ethereum, new blockchains prioritizing security over speed.
For Speed & Efficiency
Choose BLAKE2b for high throughput and energy efficiency. Ideal for payment-focused networks that need thousands of transactions per second.
Recommended for Nano, high-volume transaction systems.
For Legacy Projects
Use SHA-256 for Bitcoin-like projects where stability and compatibility are critical. Best for established networks with large user bases.
Recommended for Bitcoin, projects needing backward compatibility.
Cryptocurrency security doesn’t come from complex encryption-it comes from hash functions. These are mathematical one-way engines that turn any amount of data into a fixed-size string of characters. Change one letter in a transaction, and the hash changes completely. No one can reverse it. That’s the foundation of blockchain trust. But not all hash algorithms are the same. Bitcoin uses one. Ethereum uses another. Litecoin, Nano, and Zcash each picked their own. Why? Because each algorithm has trade-offs in speed, security, memory use, and resistance to mining centralization.
SHA-256: The Bitcoin Standard
SHA-256 is the original workhorse of cryptocurrency. It’s what Satoshi Nakamoto chose for Bitcoin in 2009, and it’s still running the largest blockchain by market cap. The algorithm takes any input-whether it’s a single word or a gigabyte of data-and turns it into a 256-bit hash, shown as a 64-character hexadecimal string. It’s fast, deterministic, and, so far, unbroken.
But speed comes at a cost. SHA-256 is optimized for ASICs-specialized mining chips. Companies like Bitmain and MicroBT now produce machines that can do 300 terahashes per second. That’s 300 trillion guesses per second. The result? Individual miners with GPUs or CPUs can’t compete. Bitcoin mining is now dominated by a handful of corporate farms in places like Texas and Kazakhstan. This centralization is the biggest criticism of SHA-256.
SHA-256 isn’t just used for mining. Bitcoin addresses are created by first hashing the public key with SHA-256, then again with RIPEMD-160. This double-hash makes addresses shorter and more secure. Even though it’s old, SHA-256 remains trusted. Bitcoin Core developers like Pieter Wuille argue that its age is its strength-after 15 years of global scrutiny, no practical collision has been found. The algorithm is battle-tested in a $500 billion ecosystem.
Keccak-256: Ethereum’s Custom Hash
Ethereum doesn’t use SHA-3. It uses Keccak-256, a variant that’s almost the same-but not quite. The difference? Padding rules. Keccak was the winner of NIST’s SHA-3 competition in 2012, but Ethereum’s team made a small tweak to the standard before launching in 2015. That tweak means Ethereum’s hashes are incompatible with official SHA3-256 implementations. It was intentional: to prevent cross-chain attacks where someone could reuse a transaction signature from one chain on another.
Keccak uses a ‘sponge construction,’ which absorbs input data and then squeezes out the output. This design makes it more resistant to length extension attacks than SHA-256. For Ethereum’s smart contracts, that’s critical. A flaw in hashing could let someone manipulate contract data. Keccak-256 is slower than SHA-256 on ASICs, but it’s efficient on GPUs. That’s why Ethereum originally relied on GPU mining and resisted ASICs for years.
After the Merge in 2022, Ethereum moved to proof-of-stake, so mining is gone. But Keccak-256 is still used everywhere else: for transaction hashing, block headers, and smart contract execution. The Ethereum Foundation now plans to switch to the official NIST SHA3-256 standard by 2025 to align with global cryptographic norms. That change won’t break anything-it’s a behind-the-scenes upgrade to improve standardization and long-term trust.

BLAKE2b: Speed for High-Throughput Networks
If you need speed, BLAKE2b is the algorithm to beat. Designed in 2012 by cryptographers including Jean-Philippe Aumasson, it’s faster than SHA-256 and even Keccak on modern CPUs. Benchmarks show it can hash data at over 1,200 MB/s on Intel Xeon processors-nearly twice as fast as SHA-256. That’s why Nano, a cryptocurrency focused on instant, feeless payments, uses BLAKE2b.
Nano’s block-lattice structure means every account has its own blockchain. Every transaction needs a quick hash to be verified. BLAKE2b makes this possible: Nano handles up to 7,000 transactions per second with under-one-second confirmations. Compare that to Bitcoin’s 4-7 transactions per second. BLAKE2b’s efficiency also means lower energy use. A 2023 study found BLAKE2-based networks consume only 0.05 kWh per 1,000 transactions. Bitcoin’s SHA-256 network uses 950 kWh for the same volume.
BLAKE2b is also ASIC-resistant by design. It’s not memory-hard, but it’s optimized for general-purpose CPUs. That means home users and small validators can still participate without expensive hardware. Developers love it too-libraries are well-documented, and implementation is straightforward. It’s not as widely adopted as SHA-256, but for new projects focused on speed and efficiency, BLAKE2b is becoming a top choice.
Scrypt and Equihash: Memory-Hard Algorithms
Scrypt and Equihash were built to fight ASIC dominance. The idea? Make mining require a lot of memory, not just raw processing power. Regular computers have plenty of RAM. ASICs don’t. So if a hash function needs 128MB or more of memory per calculation, ASIC manufacturers can’t easily build chips for it.
Litecoin, launched in 2011, was the first to use Scrypt. It required 32 times more memory than SHA-256. For a while, it worked. GPU miners could compete. But by 2018, Scrypt ASICs were everywhere. Litecoin’s ASIC resistance failed. Today, it’s just another SHA-256-style mining race, just with a different algorithm.
Equihash, created in 2016 and used by Zcash, was the next attempt. It requires 140MB of RAM per hash. That’s a lot for a phone, but manageable for a desktop. The theory was solid. But by late 2022, Innosilicon released the Z15 ASIC miner, capable of 1,500 sol/s. Zcash’s ASIC resistance collapsed. GPU mining became unprofitable. The lesson? Memory-hard doesn’t mean ASIC-proof. It just delays it.
Both algorithms are still in use, but their original goal-to keep mining decentralized-hasn’t held up. They’re now more about historical legacy than practical advantage. Newer projects avoid them unless they have a specific reason to use them.
Why Does It Matter Which Algorithm You Use?
Choosing a hash function isn’t just a technical decision. It shapes the entire economics of a cryptocurrency.
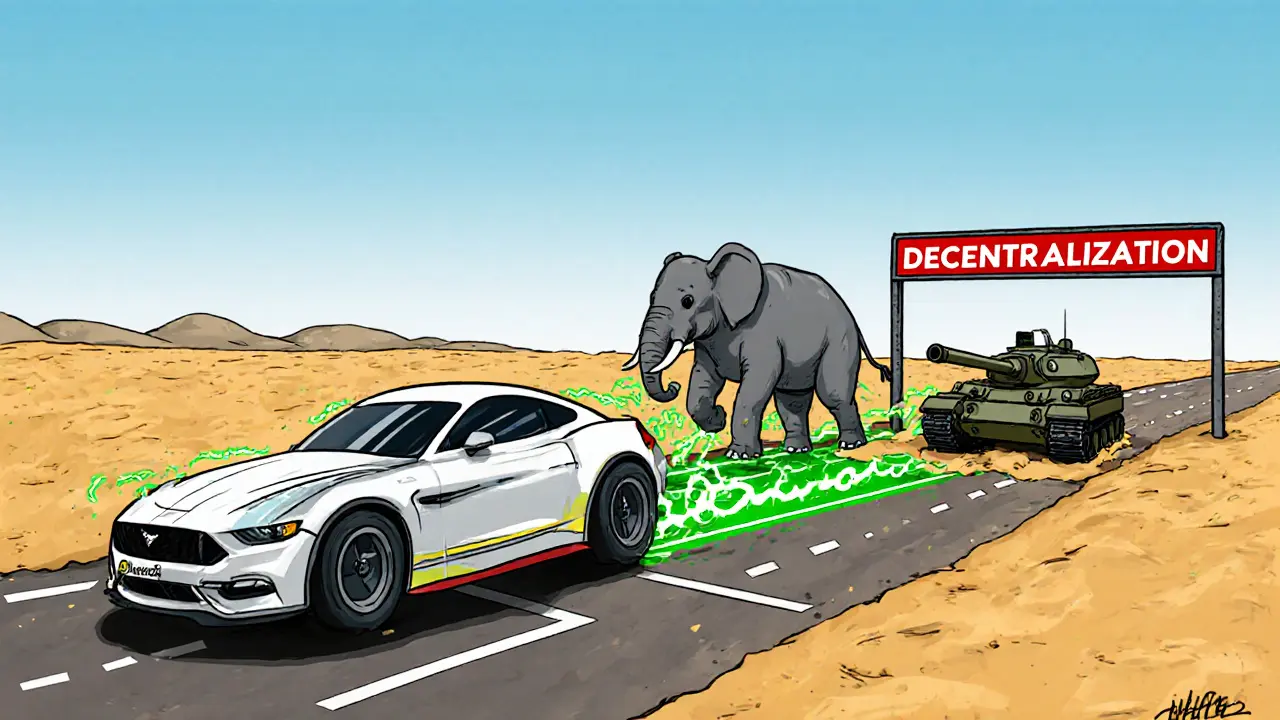
SHA-256 creates centralized mining. That’s good for security-large mining pools have strong incentives to keep the network honest. But it’s bad for decentralization. If a few companies control 80% of the hash power, the network becomes vulnerable to collusion or government pressure.
Memory-hard algorithms like Equihash tried to fix that. They failed. BLAKE2b and Keccak-256 offer a middle ground: they’re fast enough for high throughput but don’t create the same ASIC monopoly. That’s why newer chains like Solana and Avalanche use custom or optimized hashes that balance speed, security, and accessibility.
Security-wise, all the major algorithms-SHA-256, Keccak-256, BLAKE2b-are still considered secure. NIST and independent cryptographers confirm no practical collision attacks exist. But the future is changing. Quantum computing could break SHA-256 in 10-15 years. That’s why Ethereum is moving toward SHA3-256. And why NIST is already standardizing quantum-resistant algorithms like CRYSTALS-Kyber, even if they’re not hash functions yet.
For developers, the choice affects implementation. SHA-256 has the most libraries and documentation. RIPEMD-160 is harder to find. Keccak-256 has quirks in padding. BLAKE2b is clean and fast. If you’re building a new blockchain, your algorithm choice affects your developer onboarding, security audits, and long-term upgrade path.
What’s Next for Hash Algorithms in Crypto?
The future isn’t about replacing SHA-256 overnight. Bitcoin won’t change its hash function. It’s too entrenched. But new projects are already moving on.
By 2027, Gartner predicts 30% of new blockchains will use SHA-3 variants. That’s up from 12% in 2023. Why? Quantum resistance. Even if quantum computers aren’t here yet, the threat is real. Harvesting attacks-where attackers store encrypted data now to decrypt later-are already a concern.
Algorithm agility is becoming a key design principle. Projects like Cardano and Polkadot are building systems where the hash function can be upgraded without hard forks. That’s the real innovation: not picking the perfect hash today, but designing a network that can adapt tomorrow.
For now, SHA-256 still powers nearly half of the crypto market. But the tide is turning. The next generation of blockchains won’t just be faster or cheaper. They’ll be built on hash functions designed for a world where quantum computing, global regulation, and decentralized access all matter.
What is the most secure hash algorithm for cryptocurrency?
All major algorithms used today-SHA-256, Keccak-256, and BLAKE2b-are considered cryptographically secure. No practical collision attacks have been demonstrated against any of them. SHA-256 has the longest track record, having been used in Bitcoin since 2009. Keccak-256 offers better resistance to certain types of attacks like length extension. BLAKE2b is faster and more efficient. For long-term security, especially with quantum computing on the horizon, SHA-3 (Keccak) is seen as the more future-proof choice by many researchers.
Why does Bitcoin use SHA-256 and not a newer algorithm?
Bitcoin uses SHA-256 because it was the best available option in 2008-2009. It was standardized, well-understood, and had no known weaknesses. Changing it now would require a hard fork, which would split the network. Bitcoin’s developers prioritize stability and consensus over theoretical improvements. The algorithm has been under constant attack for 15 years and remains unbroken. For Bitcoin, proven reliability outweighs the benefits of newer alternatives.
Can hash algorithms be hacked?
Hash functions themselves aren’t encrypted data-they’re deterministic functions. You can’t "decrypt" a hash. The only way to break them is to find two different inputs that produce the same output (a collision). While MD5 and SHA-1 have been broken this way, SHA-256, Keccak-256, and BLAKE2b have not. The cost to find a SHA-256 collision today is estimated at $2^55, which is still far beyond what any single entity can afford. For now, these algorithms are effectively unhackable through brute force.
Why do some cryptocurrencies use multiple hash functions?
Bitcoin is the main example: it uses SHA-256 for mining and block verification, then RIPEMD-160 for address generation. This two-step process reduces address size and adds an extra layer of security. If one algorithm were compromised, the other might still hold. Other chains use multiple hashes for different roles-like one for transactions and another for smart contracts. It’s about layering security and optimizing for specific tasks.
Is SHA-3 better than SHA-256 for future blockchains?
Yes, for new projects, SHA-3 (Keccak-256) is generally preferred. It has a different internal structure (sponge construction) that makes it more resistant to advanced cryptanalytic attacks. It’s also the NIST standard for post-quantum readiness. While SHA-256 is still secure, SHA-3 is designed with modern threats in mind. Ethereum’s move toward SHA-3-256 by 2025 shows this trend. For new blockchains, choosing SHA-3 signals a commitment to long-term security and adaptability.

Wow this is wild. I just mined Litecoin on my laptop in 2013 and now I see it's all ASIC farms. Feels like watching a neighborhood turn into a Walmart.
I love how we treat hash functions like they're gods... SHA-256? Sacred. Keccak? Divine. BLAKE2b? The forgotten prophet... But honestly, it's all just math with a cult following. We're not building blockchain-we're building religion with code.
So... let me get this straight... they say SHA-256 is 'unbroken'... but what if the NSA just didn't tell us they broke it? And now they're sitting on 80% of the hash power? And Ethereum's 'upgrade' is just a distraction so they can quietly backdoor the whole thing? I'm not paranoid-I'm PREPARED.
This is why crypto is a scam. Everyone's so busy arguing about hash functions they forget no one cares about the tech-they just want to get rich.
Let's be real: SHA-256's ASIC centralization is a feature, not a bug. You want decentralization? Go mine on your toaster. The market rewards efficiency. If you can't compete, you're not a miner-you're a hobbyist with a GPU fetish.
US built SHA-256. China built the ASICs. Ethereum? Made by crypto bros who can't spell 'cryptography'. BLAKE2b? That's some EU tech bro nonsense. Real men mine Bitcoin. The rest are just noise.
I’ve been following this since 2014. What’s beautiful isn’t the algorithm-it’s the fact that people from Lagos to L.A. are all using the same math to trust each other without a bank. That’s the real miracle. Not the hash. Not the chain. The trust.
This is actually very well explained. I’m from Nigeria and we use crypto because our banks are unreliable. The hash function doesn’t matter to us-what matters is that the transaction goes through. Thank you for making this clear.
I think we're overcomplicating this. Pick the fastest, most efficient one. Let the market decide. No need for drama.
It's funny how we treat these algorithms like they're alive. SHA-256 is the old warrior. Keccak is the wise student. BLAKE2b? The quiet genius who just wants to get things done. We’re not choosing crypto tech-we’re choosing philosophies.
Bro let me break this down for you 🤓 SHA-256 = slow but safe = Bitcoin = old school dad. Keccak-256 = sponge magic = Ethereum = the overthinker who reads 10 papers before breakfast. BLAKE2b = turbo mode = Nano = the guy who finishes his coffee in 3 seconds and already left. Scrypt? That’s the guy who bought a Tesla but forgot to charge it. Equihash? The one who thought he could outsmart ASICs with a backpack full of RAM. Spoiler: he couldn't. Quantum? That’s the guy who just showed up with a lightsaber and said ‘y’all good?’ 🌌
Honestly? I just want my transactions to be fast and cheap. I don't care if it's SHA-256 or SHA-999. As long as it works.
The real issue isn’t the hash-it’s that we keep pretending decentralization is a technical problem. It’s a human one. No algorithm can fix greed.
I think you meant RIPEMD-160 not RIEPMD-160... wait no I'm not even sure what I'm reading anymore. My brain is fried from crypto tweets.
Let’s be honest: SHA-256 is the only algorithm that matters because Bitcoin is the only cryptocurrency that has value. Everything else is just speculative vaporware dressed up with fancy math. BLAKE2b? Cute. Keccak? Adorable. But only SHA-256 has the network effect, the brand, the market cap. The rest are academic footnotes.
You're all missing the point. The real power isn't in the hash-it's in the fact that people believe in it. That's the only thing that's ever moved markets.
So we're spending billions to protect a hash function that might be broken by a quantum computer in 10 years? We're building a castle on a sand dune and calling it 'decentralized'.
I used to think the algorithm mattered. Now I just look at who controls the mining. If it's a few companies in Texas and Kazakhstan? That's not decentralization. That's just corporate power with a blockchain sticker on it.
The real innovation isn't algorithmic agility-it's governance agility. The ability to upgrade cryptographic primitives without fracturing consensus is the true test of a blockchain's maturity. SHA-256's immutability is its strength and its prison.