The Core Problem of Digital Trust
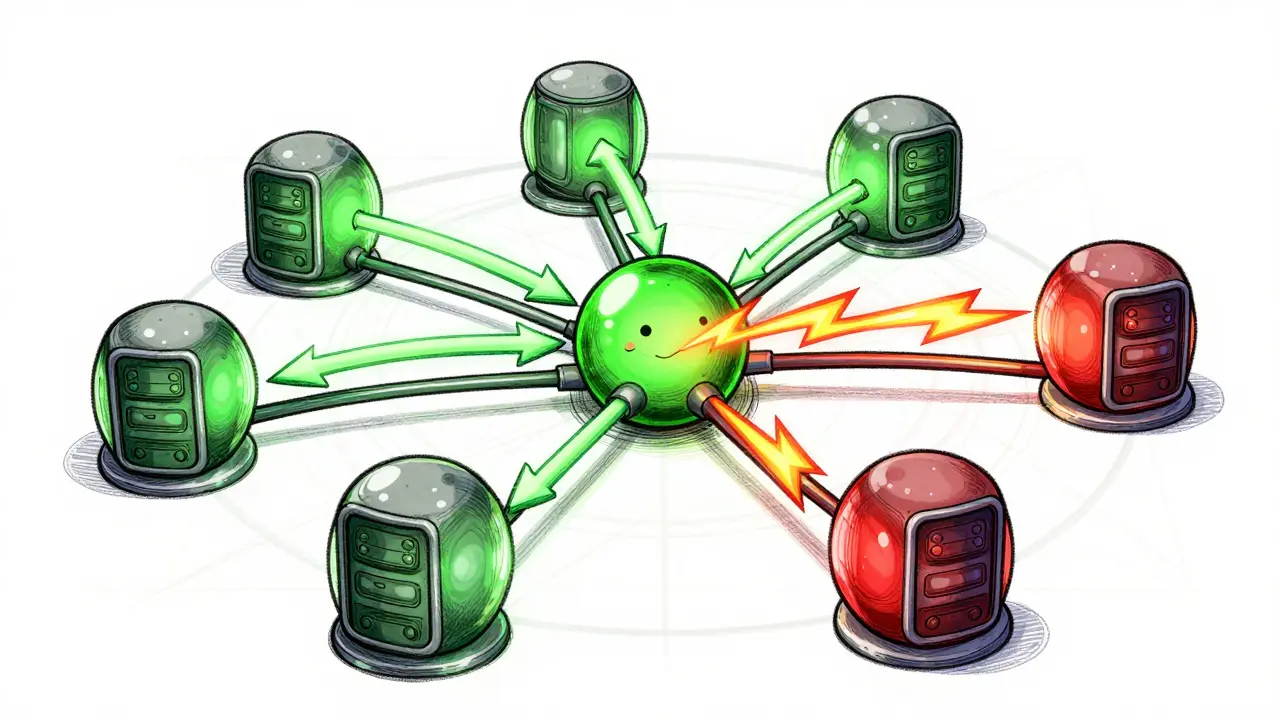
Imagine you're leading a group of generals surrounding a city. You need to agree on when to attack, but some generals might be traitors sending false messages. If one general says "attack" while another says "retreat," the entire mission fails. In computer science, this isn't just a hypothetical scenario; it's the central challenge of building reliable systems. We call this the Byzantine Generals Problem, a fundamental issue in distributed computing where nodes must reach agreement despite potential malicious actors. The solution to this problem determines whether your system crumbles under betrayal or stands firm.
This reality divides consensus mechanisms into two distinct camps. On one side, you have Byzantine Fault Tolerance, or BFT. On the other, you have Traditional Consensus. While they sound similar, the gap between them defines who can run your network, how fast it moves, and how safe your data really is. Most people assume all blockchains work the same way, but understanding these differences explains why some systems prioritize speed over security while others do the opposite.
What Exactly Is Byzantine Fault Tolerance?
Byzantine Fault Tolerance isn't just a feature; it's a specific property that allows a distributed system to function correctly even when some components act maliciously. When we talk about Distributed Systems, we mean networks where no single entity holds all the control. In a BFT environment, the system guarantees safety and liveness regardless of what bad actors try to do. This means the network continues operating securely even if up to one-third of the nodes are compromised, lying, or sending conflicting information.
The math behind this is precise. For a system to tolerate $f$ Byzantine faults, it needs at least $3f + 1$ total nodes. This ensures that honest nodes always outvote the malicious ones. Practical Byzantine Fault Tolerance, often shortened to pBFT, is the most famous implementation of this concept. It was developed to handle arbitrary failures rather than just simple crashes. Unlike standard crash-fault tolerance, where a machine just stops working, a Byzantine node might actively sabotage the network by broadcasting incorrect transaction records or voting twice in the same round.
In the context of Blockchain Technology, BFT is critical because there is no central administrator to fix mistakes. Every Node must agree on the state of the ledger. Without BFT, a hacker controlling a few nodes could alter history or double-spend funds, destroying the value of the asset.
Understanding Traditional Consensus Mechanisms
Before BFT became popular in crypto circles, engineers used traditional consensus algorithms for decades. These include well-known protocols like Paxos and Raft. These mechanisms excel in environments where participants are trusted. They assume that machines might break down or lose power-known as crash failures-but they do not anticipate that a participant will intentionally lie.
Raft, for instance, is designed for internal corporate databases. If a server stops responding, the leader election process picks a new head without asking questions. The logic assumes that hardware is the enemy, not human malice. Because of this assumption, traditional consensus requires only a simple majority-more than 50% of the nodes-to make decisions. This makes it much faster and requires less communication overhead compared to BFT protocols, which demand a supermajority of roughly 67% to guarantee safety.
The distinction matters immensely for deployment. If you are building a private cloud cluster where you own every server, using Raft is efficient. If you are launching a public cryptocurrency, Raft is dangerous because anyone can join the network, meaning you cannot trust that 51% of the voters are honest.
Comparing Performance and Complexity
When evaluating these systems, performance often comes down to message complexity. In Consensus Algorithms, nodes talk to each other constantly to agree on the next step. Traditional mechanisms like Raft typically achieve O(n) message complexity. As the number of nodes grows linearly, the amount of chatter grows proportionally. This allows for high scalability in known networks.
| Feature | Byzantine Fault Tolerance (BFT) | Traditional Consensus (Raft/Paxos) |
|---|---|---|
| Fault Model | Malicious or Arbitrary Failures | Crash Failures Only |
| Tolerance Limit | Up to 1/3 Malicious Nodes | Any Minority Failure |
| Message Complexity | O(n²) High Bandwidth |
O(n) Low Bandwidth |
| Typical Latency | Higher due to Verification Rounds | Lower, Faster Convergence |
| Use Case | Public Blockchains, Cross-Organization | Internal Clusters, Cloud Infrastructure |
BFT algorithms generally require O(n²) messages. Every node often needs to verify information with every other node to ensure no traitor is hiding. As the network expands, the bandwidth requirement explodes exponentially. This is why pure BFT doesn't scale easily to massive public networks without modifications. A classic review of distributed systems highlights that while BFT offers superior security guarantees, the computational overhead is significant. Engineers must sacrifice raw throughput to maintain absolute truth against attacks.
However, modern improvements are changing this landscape. Ethereum, for example, uses a variation of Proof of Stake combined with gossip protocols to optimize this communication. Still, the fundamental bottleneck remains: verifying truth costs more resources than assuming innocence.
Implementation Strategies in Modern Networks
Real-world applications rarely rely on a single textbook algorithm. Security researchers note that pure BFT implementations face challenges in global public networks due to latency issues. Instead, many systems adopt hybrid approaches. They might use a Delegated Proof of Stake (DPoS) mechanism to select a small committee of validators, effectively reducing the 'n' in the equation. By limiting the number of active voters to a manageable size, they retain the security benefits of BFT while mitigating the bandwidth explosion.
Another strategy is seen in permissioned blockchains. Organizations like Hyperledger often deploy BFT variants where the identity of all participating nodes is known and vetted. Since participants are verified companies, the threat model shifts closer to traditional consensus, allowing for higher performance. Conversely, permissionless networks like Bitcoin rely on computational difficulty. Bitcoin does not use classical BFT voting. Instead, it creates economic disincentives through mining costs. Yet, the end result-resistance to adversarial behavior-is effectively a form of Byzantine fault tolerance achieved through economics rather than cryptographic signatures alone.
Economic incentives play a huge role here. In Proof of Stake systems, validators stake their tokens. If they behave maliciously, they get slashed, losing their investment. This aligns the behavior of the nodes with the health of the network. It transforms the theoretical math of BFT into a financial reality. The risk of financial loss acts as a check against the chaotic nature of Byzantine faults.

Choosing the Right Mechanism for Your Needs
Selecting the right consensus engine depends entirely on your threat model. If you are managing an internal database for a hospital, you want speed and simplicity. Using a heavy BFT protocol would waste time verifying identities that you already control. In these cases, Raft provides excellent reliability with low latency.
If you are building a cross-border payment platform involving competing banks, you need Byzantine Fault Tolerance. None of the banks fully trust the others, so the system must survive if one decides to cheat. Here, the cost of communication is acceptable compared to the cost of corruption. Similarly, decentralized finance platforms prioritize security above all else, accepting slower transaction times to prevent fund theft.
The industry is moving toward adaptive solutions. Some new protocols adjust their consensus requirements dynamically based on network conditions. During low-traffic periods, they might enforce stricter Byzantine rules, while in high-throughput scenarios, they rely on sampled subsets of validators. This flexibility helps bridge the gap between the high security of BFT and the efficiency of traditional models.
Future Trends and Research Directions
Research from institutions like the University of Toronto indicates a clear shift. Developers are moving away from viewing BFT as a rigid rulebook and toward treating it as a set of properties that can be layered. Sharding is a prominent technique emerging from this. By splitting a large network into smaller chunks (shards), each shard can run its own consensus process. This reduces the effective 'n' significantly, making Byzantine agreement feasible on a larger scale.
Furthermore, advancements in zero-knowledge proofs are helping validate transactions without revealing underlying data, adding another layer of privacy and verification. As quantum computing looms on the horizon, both BFT and traditional consensus mechanisms will face new mathematical challenges. Post-quantum cryptography standards are being integrated now to future-proof these algorithms against advanced decryption threats.
The evolution is clear: we don't need to choose between perfect security or perfect speed anymore. The goal is resilience. Systems will likely become more modular, using BFT for critical checkpointing and traditional methods for routine state updates. This architecture provides the best of both worlds, ensuring that digital trust remains robust even as the world becomes increasingly unpredictable.
Frequently Asked Questions
Why does BFT require 3f+1 nodes?
This formula ensures that honest nodes always outnumber malicious ones even if a fraction ($f$) of the total network behaves arbitrarily. With $3f + 1$ total nodes, you guarantee that $2f + 1$ honest nodes remain, preventing bad actors from forging consensus.
Is Bitcoin considered a BFT system?
Technically, Bitcoin achieves Byzantine fault tolerance through Proof of Work rather than explicit BFT voting protocols. The computational energy cost secures the network against attacks, effectively solving the same problem via different means.
Can Raft be used in a public blockchain?
No, Raft relies on the premise that nodes fail by crashing, not by lying. In a public network where anonymous nodes might act maliciously, Raft cannot guarantee safety, making it unsuitable for open blockchain applications.
How does BFT affect transaction speed?
BFT protocols generally introduce higher latency because nodes must wait for multiple rounds of messaging and confirmation from peers to detect faults. This results in slower finality compared to simpler crash-tolerant systems.
What is the difference between Crash Fault and Byzantine Fault?
Crash faults occur when a node stops working completely, whereas Byzantine faults involve a node behaving unpredictably or maliciously. Handling Byzantine faults requires verifying data integrity, which is much harder than detecting silence.

I beleive the governement is watching thse nodes 😱 They want controll over your private key and destroy the free market system that is supposed to exist here. It is obvious that the bad actors are planting false flags in the consensus mechanisms to make us doubt our own eyes. We cannot trust these numbers because the elites are pulling strings from behind the curtain. Everyone should read between the lines carefully before trusting any blockchain protocol. 😡
The mathematical requirement for three f plus one nodes guarantees safety against arbitrary failures in asynchronous networks. Traditional crash fault tolerance protocols simply cannot handle malicious deviations from the defined state machine. Paxos assumes rational behavior whereas BFT accounts for adversarial manipulation of data packets during transmission.
People really think they understand distributed systems after reading one article. You guys are still arguing about theoretical models while the market crashes. 🙄 It's cute but the real world doesn't wait for perfect math proofs. Just pick one and move on before inflation eats your wallet.
I feel sad that you dont trust anyone anymore. Trust is love not math equations. Why do you think everyone is trying to hurt you? It makes my heart break to see this fear online today.
I have been thinking about how sharding changes everything in the landscape. It is amazing what people believe about blockchains being the absolute solution. Many think proof of work is the only way but it burns energy unnecessarily. We need new ways to validate transactions quickly without lagging behind. If you look at the math the latency drops significantly over time. Sharding breaks the network into smaller groups to process data faster. Each group works independently to verify blocks without central oversight. This reduces the load on every single node hardware significantly. But security might suffer if one shard gets compromised easily. That is why cross shard communication is so hard to get right. Developers are still working on solving that problem efficiently. Zero knowledge proofs help hide data while validating it simultaneously. Privacy becomes a huge part of the equation now for everyone. Eventually we will not see this split anymore between systems. Systems will adapt dynamically based on traffic levels automatically.
This article is boring and does not explain anything new.
The essence of digital trust is a philosophical journey into the nature of human cooperation. When we build machines that agree we are projecting our desire for harmony onto silicon. It is beautiful to watch abstract concepts become tangible code. The universe seeks balance through equilibrium and consensus mimics this cosmic dance perfectly. We are merely observers of these grand mechanical ballets unfolding in binary streams.
We should focus on bringing people together through technology rather than fighting. Understanding these differences helps us build bridges between different systems. It is wonderful to see innovation moving forward at such a pace. Let us all work towards a brighter future for global connectivity and peace. Together we can solve these complex challenges efficiently.
Trust nobody they are lying to you. These algorithms are rigged to favor the banks and big corporations. Wake up sheeple before its too late for everyone. 💀👁️🗣️
i totally agree with that perspective and it makes sense why we need better security layers now. Its crazy how fast things change in this industry we live in. Hope we can fix the issues soon enough for everyone involved.
the distinction drawn here is superficial and lacks depth regarding cryptographic primitives required for actual implementation. one must consider the computational complexity classes involved in verification processes. furthermore the latency metrics cited are highly variable across different network topologies. rigorous peer review is essential before accepting these generalized statements.
You bring up some very important points about the complexity there. I respect how detailed you are being with the analysis of the topic. It would be nice to see more research on this subject in the near future.